As we attain the top of 2017, it’s not possible to not look again on a 12 months within the drone trade with out recognizing the ups and downs of main producer, DJI. Most of the ups have in fact been product-related: The Spark hit the market, as did the CrystalSky screens, Mavic Pro iterations, DJI Goggles and a variety of latest cameras and equipment.
Most of the downs have been associated to knowledge safety, from US Army memos to ICE paperwork and a turbulent bug bounty program. In 2017, DJI has cemented its place because the main provider to each leisure pilots and professionals. But with that domination has come extra scrutiny. This previous 12 months the corporate has been beneath the microscope greater than ever, which isn’t in itself a adverse factor. With nice energy comes nice duty, in any case.
Michael Perry, managing director of North America for DJI, sat down with Ian Smith of the Commercial Drones FM podcast for an in-depth dialog on all the above and extra. Among the matters coated have been:
- Drone re-registration
- New merchandise – AeroScope and FlightHub
- U.S. Army memo & Local Data Mode
- Bug bounty program
- U.S. and non-U.S. server places
- ICE Report on DJI drones “sending critical U.S. infrastructure data back to China”
- DJI’s position within the drone trade transferring ahead
But we’re going to concentrate on the information safety matters. Not as a result of they’re essentially the most attention-grabbing essentially, simply because it’s good to finish the 12 months with the hope that we will discuss one thing else come January…
So what did Michael Perry need to say on:
The US Army memo that circulated over the summer season…
It’s attention-grabbing to listen to Perry’s ideas on the US Army memo, which was arguably the catalyst for a variety of tales and bulletins that adopted. In case you don’t bear in mind, the memo really helpful that each one army use of DJI drones be halted, as a result of ‘Cyber Vulnerabilities‘.
Most attention-grabbing is the truth that DJI nonetheless has no thought what ‘cyber vulnerabilities’ the memo was referring to. Although there are some things the memo might have been referring to. Here’s what he needed to say:
“The military memo typically was speaking about ‘cyber vulnerabilities’, and we’ve not seen the report that they’ve cited in Army analysis lab or Navy analysis lab memos that they’ve cited within the report. So we don’t know what they’re responding to particularly. They have been simply speaking about ‘cyber vulnerabilities’ as a bigger bucket.
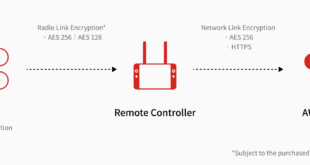
“To our mind that that could be one of two things. One is about the safety of the integrity of the data that’s collected by the drone or you know the ability for malicious actors to attack the drone while it’s in operation.”
Local Data Mode…
Interestingly, Perry reveals that each the Bug Bounty program and the Local Data Mode that adopted have been truly in growth earlier than the memo went public. Although ‘in progress‘ might imply something from an idea on a whiteboard to beta testing.
“The two announcements that you were talking about were actually things that were in progress ahead of that memo, just because they were challenges that we anticipated earlier this year… we ended up having to accelerate the announcements just to show ‘hey look, we’re working on these things’.”
Perry says that Local Data Mode was led to by enterprise purchasers’ requests for absolute safety.
“Local Data mode actually came out of a request from over a year ago when we were working with some of our enterprise clients, who said ‘Look, I understand that DJI has the ability to capture flight logs and can upload pictures and videos to Skypixel’. We’ve done a lot of work to help show that that’s a manual operation that people have to opt into.”
According to Perry, the truth that flight logs needed to be manually uploaded was not convincing sufficient for some clients, notably these coping with delicate operations.
“We demonstrated that to the client and they said, ‘Okay, got that. It’s not being passively pulled to someplace else. But we also know that a lot of the operators in the field using your equipment might accidentally push a button that they’re not supposed to and there are OPSEC requirements in terms of how they handle data.”
“We started doing that over a year ago… And earlier this year we started getting that request more frequently from our enterprise customers. So it was a priority for us to start rolling this out sooner rather than later.”
The places of DJI’s servers…
Part of the perceived cyber vulnerability of DJI drones and software program was most likely as a result of query marks over the placement of the corporate’s servers and the notion that drones are sending delicate data to China. Here’s what Perry needed to say on this concern:
“Obviously, as a global company, we have servers all over the world. That includes Amazon Web Services servers here in the US. So when somebody uploads their data to DJI, that’s stored on an AWS server. American users, when they upload something to DJI, it’s stored on an AWS server here in the States.”
So that’s about as particular as he might have been about the place American pilots’ manually uploaded knowledge goes.
Typically, he says, this data is saved for the sake of customer support. When someone crashes their drone or has a technical concern, DJI can check out the flight logs and decide what occurred.
Adapting to the duty that comes with being greater than a shopper firm…
There are two faculties of thought surrounding DJI and the corporate’s knowledge safety points. On the one hand, a vocal minority imagine that the actions of the Chinese producer are nefarious, a menace to nationwide safety and quantity to espionage.
More seemingly – and one thing that’s eluded to by Perry – is the truth that DJI is having to adapt to knowledge duties that include having an enormous variety of enterprise purchasers. There have been teething issues:
“As we’re moving into a more enterprise field we’re having to step up our data security game. We have to start thinking about how large companies are using software to capture and store data, and I think that’s not a unique challenge for DJI. You know several other consumer electronics categories have had to deal with the same issues.”
“That includes smartphones. As you probably know it wasn’t until the iPhone 5 that phones were accepted on military bases. And you know even still there’s that segmentation between that consumer technology which is the iPhone, and specific applications where you have to use a Blackberry even now because of the level of encryption. So I think DJI is finding our role within that.”
The Bug Bounty Program…
DJI’s rollout of a Bug Bounty program hasn’t been a clean one. Things got here to a head in November, when a safety researcher walked away from a $30ok bounty and claimed that DJI had despatched him authorized threats. Here Perry is barely contradictory.
On the one hand, he states that the Bug Bounty program was in response to the information that DJI drones have been being hacked to get round no-fly zones and altitude limits. There was no formal channel for researchers who needed to assist with this concern and that wanted to be addressed.
But he additionally admits that the announcement of the rollout got here earlier than the mandatory infrastructure was in place. Reading between the strains, the Bounty Program was rushed to assist DJI seem like it was taking safety severely – so it will possibly’t have been that far alongside when it comes to growth. Perry means that this led to a mismatch in expectations between the corporate and researchers submitting studies:
“The frustrating thing to us was that we didn’t have a formalized channel for people to let us know that there was a problem. And that’s a challenge for us as an organization because we have to be able to be able to respond to some of the potentially malicious attacks against our systems.”
“So we started talking about creating a bug bounty to respond to that specifically and then again talking about this broader bucket of cyber vulnerabilities. We wanted to provide a mechanism in case this was one of the key concerns that some of our users had about our equipment. We wanted to show that we’re doing due diligence.”
“Unfortunately, the announcement proceeded a lot of the necessary infrastructure in order to make that sort of system work. So, particularly in the early days of that program, there was a mismatch of expectations between the DJI side and the security researchers’ side. I won’t go into the specifics of Kevin’s case but I would just say that generally at that early stage there is just a total mismatch of expectations.”
“But now we have implemented a formalized terms o the agreement. We’ve set up a website and as of today we have had over 25 successful bounty claims through the program and again from researchers from all over the world”.
That ICE memo…
The remaining subject of curiosity that was coated within the interview was the ICE memo that circulated and made headlines final month. In impact, the memo said that DJI was passing on knowledge to the Chinese authorities – a notion the corporate dismissed as “insane” on the time.
Perry took the chance to set a couple of issues straight:
On claims that knowledge on US important infrastructure was being despatched again from DJI drones and made accessible to the Chinese authorities, he stated, “Categorically no. That is not true.”
“If you read the full report, you’ll see that all of it is based on one unidentified source, who apparently has deep knowledge of the drone industry. But if you start actually looking through some of the specifics of what this source is claiming, it’s pretty outrageous.”
“I mean the claims range from the small and insignificant the pretty large misses. Like saying that Yuneec and Parrot are no longer manufacturing, that we’ve (DJI) sold X amount of units shipped through this port that don’t match our numbers for what we actually sell. And the even more outlandish claims, like that our systems do facial recognition even when the system is turned off.”
“And all that’s actually onerous to abdomen. So that’s the idea on which this report is coming from which is an unidentified, unreliable particular person. That stated, we’ve to ensure that we’re addressing the considerations systematically. And that’s an space the place we’ve to do higher. We need to be clear about what we do and what we don’t do. And the simplest protection that we will level to proper now could be simply saying DJI doesn’t need your knowledge.”
“We’ve provided a ton of tools in order to make sure that you don’t give us your data that includes you know making sure that you can fly without an internet connection. But more fundamentally, we do have to do a better job to show how people’s data is being managed when it comes to DJI and that’s something that we’ll be working on through 2018.”
Final ideas
It’s actually an attention-grabbing interview and effectively value listening to. Although it’s a delicate dialog and it could possibly be mre difficult at factors, it’s good to listen to Perry admit (though in a roundabout way) that errors have been made on the subject of the Bug Bounty program and DJI’s communication normally relating to knowledge safety.
But in some ways, slip-ups are to be anticipated. Broadly, all the current steps – establishing AWS servers, Local Data Mode, trying a working Bug Bounty Program – ought to go an extended option to reassuring leisure and enterprise clients as we head into 2018.
Hopefully it received’t be too lengthy earlier than the main target shifts in direction of the positives that DJI brings to the drone desk: innovation, new hardware, software program developments and growing trade recognition.
 Unmanned Aerial Vehicle The latest drone news
Unmanned Aerial Vehicle The latest drone news