As the anti-drone industry grows, the many ways tech is used to down unmanned aircraft expands. Case in point — a research team at Johns Hopkins University recently demonstrated a hacking technique that joins a myriad of anti-drone solutions already out there – radar rifles, “virtual security domes,” acoustic detectors and more.
As the anti-drone industry grows, the many ways tech is used to down unmanned aircraft expands. Case in point — a research team at Johns Hopkins University recently demonstrated a hacking technique that joins a myriad of anti-drone solutions already out there – radar rifles, “virtual security domes,” acoustic detectors and more.
Working with a team of students, Dr. Lanier Watkins, a cybersecurity research scientist at Johns Hopkins University, unveiled a trio of security exploits that crashed a Parrot.
“We found three points that were actually vulnerable, and they were vulnerable in a way that we could actually build exploits for,” Watkins said in a university press release. “We demonstrated here that not only could someone remotely force the drone to land, but they could also remotely crash it in their yard and just take it.”
In the first hack, the exploit bewilders the BeBop by barraging it with thousands of rogue network requests via a wireless bubble. In essence, the hack talks the BeBop to death.
Watkins’ team also sent the BeBop a very large data packet — again overloading the drone’s software and processor with the same result – the kiss of dirt. A third hack fooled the BeBop into thinking the hackers’ laptop its remote control. “It severed its own contact with the drone, which eventually led to the drone making an emergency landing.”
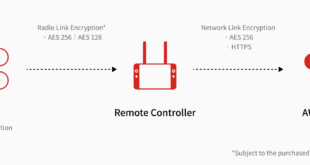
Although the security exploit is not strictly an anti-drone product, Watkin’ team demonstrated how vulnerable drones can be killed using the same techniques as commercial drone busters.
In addition to companies with viable anti-drone products, white-hat hackers like the Johns Hopkins team are publicizing the need to address both drone security and the need to protect airspace from unauthorized aircraft – goals that responsible UAV users welcome.
In May, Army Cyber Warfare officer Brent Chapman revealed a homegrown product that uses a Raspberry Pi mini-computer, a Wi-Fi card, open source software and a tin can to take down Wi-Fi-dependent drones.
“You see it with a lot of new technology,” Watkins said. “Security is often an afterthought. The value of our work is in showing that the technology in these drones is highly vulnerable to hackers.”
Source link
 Unmanned Aerial Vehicle The latest drone news
Unmanned Aerial Vehicle The latest drone news