The break-neck adoption of Internet of Things (IoT) structure throughout each industrial sector is blossoming – and that actually applies to drones. A latest examine predicted greater than half of all newly developed enterprise processes will embody IoT by 2020.
Emerging safety threats go hand in hand with rising expertise. Drone skilled Amit Ganjoo believes the drone should mount an efficient offense to defend in opposition to inevitable safety assaults between IoT units and UAVs.
“We as an industry need to consider all key technical areas and explore ways of integrating “security by design” ideas into industrial drone ecosystem improvement,” Ganjoo wrote in a latest LinkedIn article.
Ganjoo, an experimental plane builder and CEO and Founder of ANRA Technologies, says threats to drone ecosystems could be mitigated by specializing in denial of service (DoS) safety and identification administration.
As cheaper, much less dependable drones and units enter the ecosystem, Ganjoo believes such elements will show to be the weak hyperlinks that maintain the door open for devious swarms of DoS sorties.
“As more devices are connected to the wireless broadband networks, the networks will be exposed to DoS targeting the limited resources of specific services, much like botnet-driven distributed denial of service attacks in the Internet,” Ganjoo writes.
“Drones operations need to account for this possibility and plan for the mitigation of such attacks by having redundant interfaces as well as extensive fail-safes integrated in the solution.”
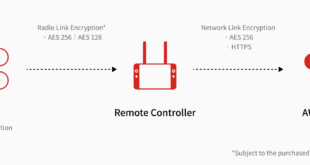
When it comes to tight drone safety, the digital transaction “knock, knock; who’s there?” could also be some of the essential interactions between drones and units. Ganjoo factors out the trade should set up and preserve stringent requirements when it comes to identification protocols throughout the tech ecosystem.
“Identifications needs exist at every layer of the stack, in every segment of the architecture,” he stated. “For example, drones might need to be identified as hardware trust anchors but then you have IP endpoints, cloud service instances, network services, virtualized network function instances, subscribers, and administrators and many more.”
Ganjoo provides that identities should “be defined, provisioned, maintained, validated, revoked, etc., so we require a robust identity management solution that captures the entire life cycle of this management task.”
Overall, Ganjoo concludes, the way forward for drone/IoT safety might be a combined bag until the industries cooperate with regulators and academia to create standardized options.
“Some segments will get higher level of scrutiny and hence security such as commercial radio access technologies such as cellular due to the standardization bodies like 3GPP. However, each segment of the overall solution has its own unique challenges that need to be looked at in detail.”
 Unmanned Aerial Vehicle The latest drone news
Unmanned Aerial Vehicle The latest drone news