Kenny Loggins’ 1980s mega-hit Danger Zone needs an update for the Age of the UAV.
Kenny Loggins’ 1980s mega-hit Danger Zone needs an update for the Age of the UAV.
How about “Highway to the Danger Drone?”
That’s music to the ears of cybersecurity consultant Bishop Fox. The company presented the Top Gun-inspired theme at the recent Black Hat USA 2016 in Las Vegas.
During the conference, Bishop Fox unleashed the Danger Drone – a “penetration testing” UAV that can attack wireless infrastructure and crack open “back doors” on targeted computer systems. The Raspberry Pi-fueled drone is inexpensive and can be constructed by beginners.
Raspberry Pi, a cheap, credit-card sized computer, is designed to connect with several “Internet of Things” devices including drones and anti-drone solutions.
iHLS.com describes the Danger Drone as “a quadcopter drone the size of a credit card that anyone with enough technical know-how can build for about $500.”
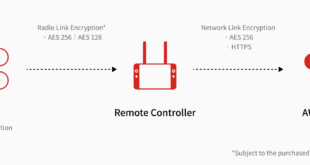
In an effort to raise awareness about possible security leaks in vulnerable systems, Bishop Fox analyst David Latimer demonstrated how the sneaky drone can attack over-the-air network protocols such as RFID, Bluetooth, and Wi-Fi.
“Drones have emerged as the prevailing weapon of choice in modern warfare, so it’s only logical that we’d also explore the potential applications of this formidable tool in cyber warfare,” Bishop Fox partner Francis Brown said in a press release.
He added that the presentation speaks to “security professionals as the target audience, helping equip pentesters with drone tools of the future (a pentester is someone who attempts to demonstrate and document security flaws).”
According to tech site Motherboard:
“The Danger Drone, when used via remote control, has a 1.2 mile (2 km) range. But with a special cellphone module the drone can be controlled via LTE, which vastly expands its range. And it can also be programmed with fixed waypoints and landing destinations.”
“It is imperative that they understand and learn how to take advantage of these attack tools and techniques to help safeguard their organizations,” Brown added.
Raspberry Pi-based tech is fast becoming a new player in the Game of Drones.
In May, army Cyber Warfare officer Brent Chapman published step-by-step directions for a home-brewed drone killer that can take down a Wi-Fi connected Parrot AR.Drone 2.0.
“The AR.Drone 2.0 is so hackable, in fact, that there are communities and competitions focused on modifying this particular drone,” he said, emphasizing pentesters should only use the anti-drone gun with permission of the drone user or in a test of their own UAVs.
Source link
 Unmanned Aerial Vehicle The latest drone news
Unmanned Aerial Vehicle The latest drone news