After information broke final week that the US Army wished to halt the use of DJI drones, loads have been leaping to the conclusion that one thing critical was up with DJI’s software program from an information safety perspective. There is no smoke with no hearth, as the saying goes. But we nonetheless don’t know the motivations behind that Army memo. And it’s unlikely that they’ll come to mild anytime quickly.
Understandably, the complete state of affairs has left DJI in an uncomfortable place and with a broken repute. Speaking to DroneLife, a US Army spokesperson has verified the doc however declined to remark additional on its contents. So the place does that go away us?
Data safety is a rising concern for DJI and its pilots.
Taking a Risk-based Approach: Is Data Secure with DJI?
Laying out the details, it’s straightforward sufficient to grasp why the US Army has taken the choice that it has. But that call might have fairly simply been made with none proof of wrongdoing on DJI’s half. So what do we all know for certain?
Data is on the Move
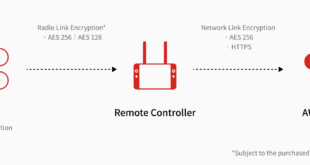
We know that DJI’s product ecosystem – which incorporates drones, flight controllers, functions and replace instruments – all document and ship info again to DJI to a sure extent.
Of course, this knowledge switch will be justified and put right down to utterly professional functions. The firm may very well be utilizing it to watch software program points, monitor the efficiency of updates or look into particular incidents. This sort of factor isn’t unusual, and also you’ll discover that almost all working techniques and main functions, akin to these from Apple and Microsoft, search permission to gather or share this sort of info to enhance their companies and merchandise.
For the overwhelming majority of pilots flying for enjoyable and initiatives, this isn’t going to be a priority. However, in the event you’re flying a delicate or labeled mission, it is likely to be sufficient to unsettle you considerably. The major concern comes because of the two issues which are distinctive to DJI on this occasion…
The China Connection: Weighing up the Risk
Speaking to DroneLife, UAS safety guide David Kovar ran by means of the points as he sees them.
“There are two problems specific to DJI,” he mentioned. First, “They are a Chinese firm with all of their IT assets in China.” And second, “The Chinese government actively and passively collects information about US Government activities along with commercial and consumer [data].”
So the conclusion is a easy one for army officers making a judgement primarily based on the dangers. The functionality is there and the demonstrated intent is there. So whether or not or not something untoward is taking place “good security practice suggests that the appropriate risk mitigation approach is to simply stop using DJI products.”
“The risk exceeds the benefit, probably by a very wide margin. I think you can argue that this is a well-considered decision even without evidence of malicious activity.”
The Unknown Quantity [of Data Transferred]
As a part of DJI’s dedication to buyer knowledge and privateness, we need to emphasize that we don’t acquire any private knowledge or info from or a few consumer, besides what the consumer chooses to manually add and share with us. The identical holds true for flight knowledge, together with any pictures or movies taken throughout flight.
However, there have been cases that recommend there is extra to DJI’s knowledge assortment than meets the eye. Since the information broke about the US Army memo, the firm has pointed to a more moderen story in The Verge suggesting that DJI drones have been confirmed protected by The National Oceanic and Atmospheric Administration.
However, there have been contradictory parts inside that article, which has since been up to date to verify that the testing used “a third-party remote and independent ground station” (ie didn’t truly check the complete DJI ecosystem) and that Ed Dumas – a pc programmer at NOAA and one in every of the authors of the research – “ran related assessments on his private unit, a Phantom three skilled, throughout his spare time. His software program discovered that unit was sending encrypted knowledge again to DJI and servers whose location he couldn’t decide.”
As Kovar factors out, “DJI has only admitted to limited data collection, either for maintenance purposes or for legal purposes. If you unlock a NFZ, for example, some additional information is collected.”
But this, he says, is the place poor communication from the firm is leaving room for conspiracies to develop. “DJI aren’t helping themselves – it is safe to assume that when you’re upgrading the firmware on your DJI product using DJI Assistant that some information is sent back to DJI: Your serial number, old firmware #, new firmware #, IP address and user account. But they didn’t mention that collection.”
Clarity is Needed
Until a radical investigation is undertaken of DJI’s product and software ecosystem, hypothesis will inevitably proceed. Kovar means that “It would help DJI’s image if they went through all of the components of their system and documented the data collection from each one in a single place.”
“Failing to mention the NFZ or the Assistant makes people wonder what else they’re not mentioning. Eventually, someone is going to do a full analysis on DJI’s system. If it doesn’t align with what DJI claims is collected, it’ll further damage DJI’s reputation.”
The Presence of Tinker: “Legitimate Malware”
It may sound innocent, however ‘Tinker’ truly represents a real risk. Over the previous day or so, a small crew together with Department 13‘s Kevin Finisterre and Andreas Makris has discovered some interesting features deep within the DJI Android application that violate Google Play’s phrases of service.
Namely, the inclusion of a Tinker patch, which successfully offers DJI the energy to ‘hotfix’ the Android software. This signifies that the app will be up to date as a background course of, with out acknowledging the consumer or having to undergo Google Play or Google Play’s security options.
This sort of patching is forbidden for good cause: It’s a straightforward means for malicious code to be loaded straight into an app with out customers realizing, and might rework an software’s conduct with a small variety of updates. It’s not the sort of characteristic you need in a drone full cease, not to mention one that you simply’re utilizing for army functions – that’s for certain.
The presence of the Tinker patch isn’t essentially proof of wrongdoing, because it’s used to replace standard apps in China akin to WeChat – albeit with hidden censorship options. But it may add performance that the consumer may not need, or permit builders to cover issues in the code at a later date.
DJI’s tech crew has been made conscious of Tinker, or quite been made conscious of its discovery, and have mentioned that it is going to be eliminated in future updates. There is no proof as of but that the Tinker backdoor has been used to patch the DJI software. But there’s additionally little doubt that its presence alone could be justification for the US Army’s choice. After all, questions stay over why it was there in the first place.
 Unmanned Aerial Vehicle The latest drone news
Unmanned Aerial Vehicle The latest drone news