Are reports of DJI Go App security problems overblown, or cause for concern?
By DRONELIFE staff writer, Jim Magill
Two related studies, released last week by a pair of cybersecurity companies, claim to reveal potential flaws in a DJI flight operation software system, which researchers say could be exploited “to target specific users with malicious updates or applications that could be used to exploit the user’s phone.”
In its response, DJI said the reports “found typical software concerns, with no evidence they have ever been exploited.” The reports are just the latest example of security issues being raised about the Chinese-based drone manufacturing and software company, which for some time has been under scrutiny by lawmakers and members of the current administration in Washington.
DJI Go App Security Problems
In a blog post Cybersecurity firm GRIMM released it findings on potential privacy concerns of DJI drones within the Android DJI GO 4 application. Researchers at GRIMM partnered with IT security company Synacktiv, which performed an in-depth dynamic and static analysis of the application.
GRIMM found the DJI GO 4 application “contains a self-update feature that bypasses the Google Play store,” and enables drone users to download and install applications via the Weibo software development kit (SDK). “During this process, the Weibo SDK also collects the user’s private information and transmits it to Weibo,” the report states.
The volume of user data available to DJI and Weibo could leave the drone user vulnerable to hacking by a malicious actor, who “may attempt to compromise DJI’s and Weibo’s servers to exploit this functionality themselves,” the report states.
In addition, the GRIMM report also notes that The DJI GO 4 application restarts itself, after the drone user tries to swipe it closed, allowing it to continue to run in the background even though the the user might believe the app is closed.
“The DJI GO 4 application contains several suspicious features as well as a number of anti-analysis techniques, not found in other applications using the same SDKs,” the report notes.
In its statement DJI said, “The hypothetical vulnerabilities outlined in these reports are best characterized as potential bugs.”
The drone developer said it has safeguards in place to prevent the download of an unofficial, or “hacked,” version of one of its apps. When it detects hacked versions of a DJI app – for example if the app has been modified to remove flight safety features, such as altitude restrictions – the company will notify the user and require the download of the more recent official version of the app from the DJI website.
If the user does not consent, DJI said it would disable the hacked version of the app.
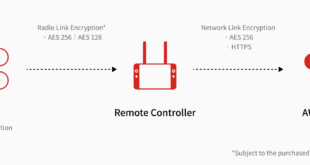
In any case, since the DJI GO4 app is primarily used as the flight operation of its recreational drones, the potential vulnerabilities described in the two reports do not extend to drones used by government agencies, the company said. “DJI’s drone products designed for government agencies do not transmit data to DJI and are compatible only with a non-commercially available version of the DJI Pilot app.”
For its recreational drones that do use the DJI GO4 app, DJI said it integrates its consumer apps with the leading social media sites via those sites’ SDKs. It referred questions about the security of the SDKs to their respective social media services. “However, please note that the SDK is only used when our users proactively turn it on,” DJI said.
The company also disputed the cybersecurity firms’ finding that DJI GO 4 was able to restart itself after being closed by the user. “We are investigating why these researchers claim it did so. We have not been able to replicate this behavior in our tests so far,” DJI said.
“We design our systems so DJI customers have full control over how or whether to share their photos, videos and flight logs, and we support the creation of industry standards for drone data security that will provide protection and confidence for all drone users.”
Over the past several years, DJI and other China-based drone companies have faced numerous questions over the security of the data collected from users. Several bills have been filed in Congress to limit the use by federal agencies of drones manufactured in, or containing components produced in, China. Earlier this year, the U.S. Department of the Interior (DOI) grounded all non-emergency operations for its entire fleet of 800 drones, citing potential security risks.
DJI, whose drones comprised a small portion of the DOI fleet, blasted the move, “which inappropriately treats a technology’s country of origin as a litmus test for its performance, security and reliability.”
In an interview, DJI spokesman Michael Oldenburg said rather than instituting a so-called country-of-origin system of drone regulation, the U.S. should establish a national set of rules regulating the cybersecurity of all unmanned aerial systems. “We’re advocating that in order to make things more secure — and it’s not just for DJI drones, but drones from any manufacturers — there should be clear and transparent guidelines and standards that those manufacturers make sure their products meet,” he said.
Miriam McNabb is the Editor-in-Chief of DRONELIFE and CEO of JobForDrones, a professional drone services marketplace, and a fascinated observer of the emerging drone industry and the regulatory environment for drones. Miriam has penned over 3,000 articles focused on the commercial drone space and is an international speaker and recognized figure in the industry. Miriam has a degree from the University of Chicago and over 20 years of experience in high tech sales and marketing for new technologies.
For drone industry consulting or writing, Email Miriam.
TWITTER:@spaldingbarker
Subscribe to DroneLife here.
https://dronelife.com/2020/07/29/dji-go-app-security-problems/
 Unmanned Aerial Vehicle The latest drone news
Unmanned Aerial Vehicle The latest drone news